As we continue our mission to provide our customers with the best vulnerability intelligence available, we observe many shifts in the landscape. We’ve seen Bugtraq fall out of favor, the rise of Patch Tuesdays, felt the full force of the Vulnerability Fujiwhara Effect, and also witnessed the rise of GitHub as a significant medium for vulnerability disclosures. But as we look back on 2021, our independent research team observed a new trend: a huge increase in the number of vulnerabilities affecting WordPress plugins.
WordPress plugin vulnerabilities up by 142 percent
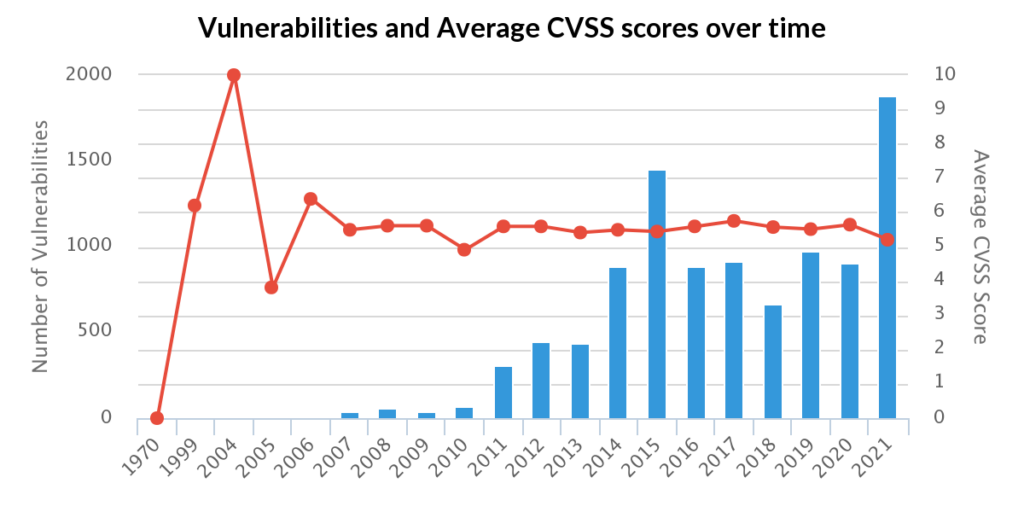
10,359 vulnerabilities were reported to affect third-party WordPress plugins at the end of 2021. Of those, 2,240 vulnerabilities were disclosed last year, which is a 142% increase compared to 2020.
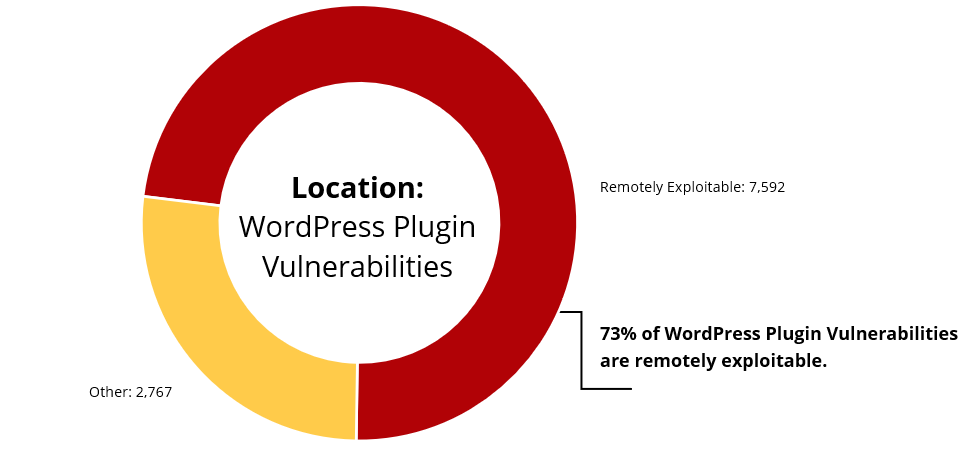
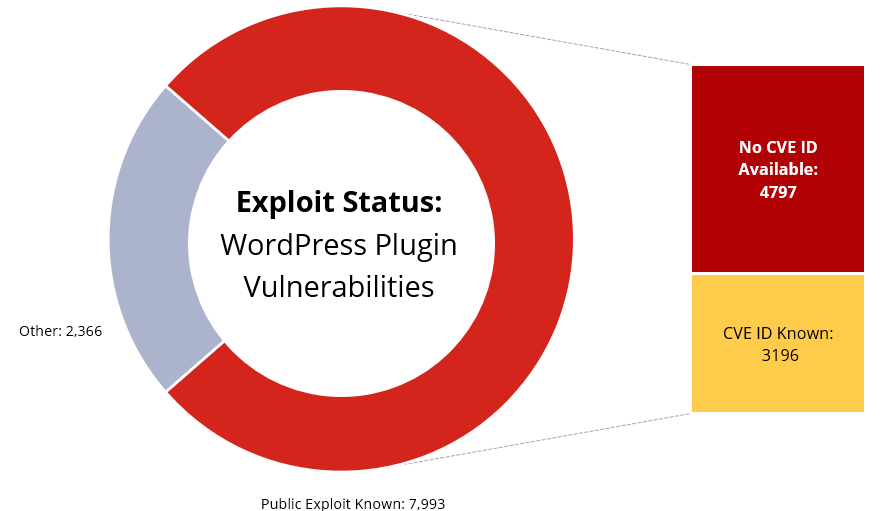
While the spike in WordPress plugin vulnerabilities is itself alarming, the primary concern is their potential for exploitation. Out of all known WordPress plugin vulnerabilities, 77% of them have known public exploits. If CVSS severity scores are the basis for your organization’s vulnerability prioritization, you may need to shift your focus to properly triage this risk.
Shift focus to exploitability, not criticality
On average, the CVSSv2 score for all WordPress plugin vulnerabilities is 5.5, which by many current VM frameworks is considered a “moderate” risk, at best. But, if you compare this data point with news headlines, you might observe a slight disconnect between conventional Vulnerability Management (VM) practices and impact.
For many organizations, vulnerabilities that have a CVSS severity score beneath 7.0 are often not considered a high priority and may get relegated to the backlog. Since the average WordPress plugin issue is scored 5.5, is it safe for organizations to instantly de-prioritize these issues? The answer is no.
We’ve been preaching this shift from criticality to exploitability for a while now, and we’re seeing some other influential organizations take note. In the most recent Gartner Security & Risk Management Summit, Mitchell Schneider, principal analyst at Gartner, encouraged organizations to make vulnerability management less about mass patching and more about prioritizing the most exploitable vulnerabilities. Recent events such as CISA BOD 22-01 also support this as they show that malicious actors are not favoring vulnerabilities with high CVSS severity scores, but are instead opting for ones that they can easily exploit.
The vast majority of WordPress plugin vulnerabilities are exploitable:
- 7,592 WordPress vulnerabilities are remotely exploitable
- 7,993 WordPress vulnerabilities have a public exploit
- 4,797 WordPress vulnerabilities have a public exploit, but no CVE ID
Securing your organization against WordPress plugin vulnerabilities
Because of factors like exploitability and attacker location, WordPress plugin issues can pose a significant threat to organizations deploying at-risk assets, even if they may not appear “highly critical” at first glance. In addition, WordPress plugin vulnerabilities may be especially dangerous for organizations relying on CVE/NVD, since they will be unaware of 60% of issues with known public exploits.
This intelligence gap is made even worse when considering the state of the WordPress plugin ecosystem. There are over 58,000 free plugins for download, with tens of thousands more available for purchase. Unfortunately, few of them are designed with security in mind, so one vulnerability could potentially affect millions of users. It will likely be a difficult undertaking for organizations to identify which of their plugins have a public exploit. While there are several companies that specialize in WordPress security that maintain their own curated plugin vulnerability databases, they still do not offer the same breadth or depth of WordPress vulnerability information that we do.
Adopting a risk-based approach
To fully understand the impact of these vulnerabilities, organizations will need to adopt a risk-based approach. Although some WordPress plugins claim to have over 500,000 installs, it doesn’t necessarily mean that all enterprises use them. Security teams will need to have knowledge of their assets, comprehensive vulnerability intelligence for all known issues, and detailed metadata, that allows them to examine factors like exploitability, to then contextualize the risk it poses to their environment.
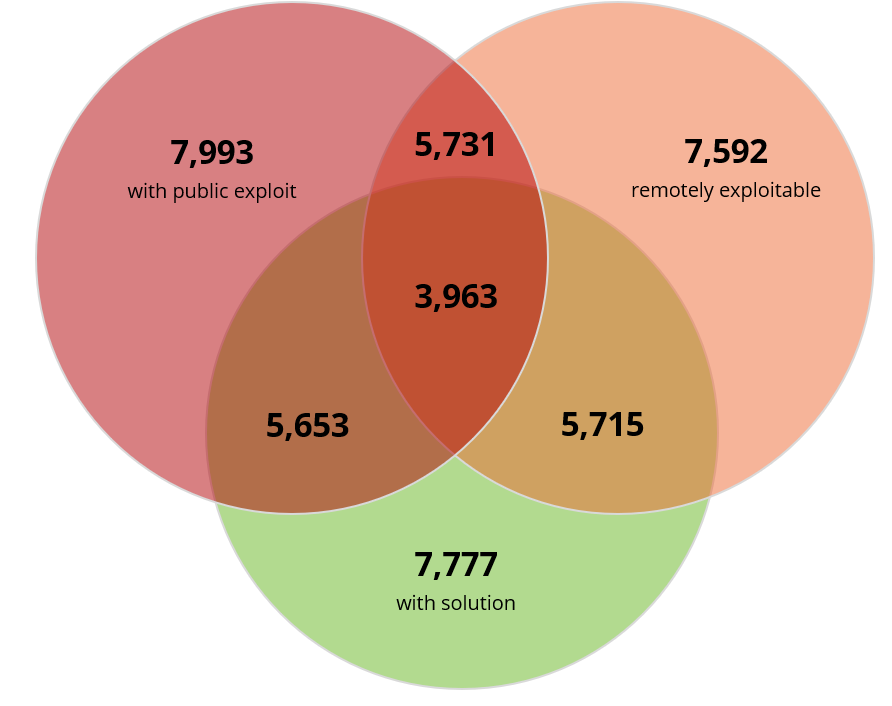
Security professionals should start with vulnerabilities that are remotely exploitable, have a public exploit, and have a known solution. And if WordPress plugin issues affect important assets, these vulnerabilities should be triaged first. By remediating these types of issues, organizations can best protect themselves against potential attacks while saving time since solution data is available. This risk-based approach will prove to be more effective than traditional Vulnerability Management models based on severity.
There are several security tools out there that focus on WordPress related vulnerabilities. However, each tool specializes in different functions meaning that organizations would have to purchase and deploy all of them to achieve maximum efficiency. Instead, organizations are better off relying on a comprehensive, detailed, and timely source of vulnerability intelligence that covers all known issues in IT, OT, IoT, and third-party libraries and dependencies. Sign up for a free VulnDB trial today.


