GLOSSARY
The Practitioner’s Guide to Vulnerability Intelligence
Security practitioners need comprehensive vulnerability intelligence. This helps them focus on the issues that matter most. However, the intelligence that many organizations rely on is likely incomplete. Find out if your current VI vendor is causing you to spend more time validating vulnerabilities rather than managing them.
Flashpoint is proud to offer industry-best vulnerability threat intelligence.
In this article we...
- Define what vulnerability intelligence is, and how it informs vulnerability management.
- Describe the vulnerability intelligence lifecycle and how it works.
- Explain the importance of vulnerability intelligence, and how your organization can gain access to a comprehensive source.
What is Vulnerability Intelligence?
Vulnerability intelligence is a specific form of threat intelligence. It focuses on gathering and sharing information about computer vulnerabilities that may put organizations at risk.
The number of software is growing quickly. As such, so too are the number of vulnerabilities. A vulnerability is a flaw in computer software or hardware. It allows an attacker to cross privilege boundaries. By taking advantage of flaws in products, threat actors can infiltrate an organization's system. They can steal sensitive data or cause damage to the network.
As such, organizations need a comprehensive source of vulnerability intelligence. This helps them better prioritize and fix risk. Ever heard of VulnDB?
The Difference Between "Good" vs. "Bad" Vulnerability Intelligence
Your vulnerability management program is completely dependent on the quality of your vulnerability intelligence. This makes it important to know what separates good intelligence from bad.
The definition of vulnerability intelligence could change depending on who you ask. Some may group vulnerability intelligence and vulnerability management concepts together. Some may even consider CVE and NVD as a comprehensive source of vulnerability intelligence.
There are clear differences between comprehensive and lacking sources of vulnerability intelligence. Many in the industry, including some practitioners, believe that the Common Vulnerabilities and Exposures (CVE) and the National Vulnerability Database (NVD) are the primary resources for disclosed vulnerabilities. This is far from the truth.
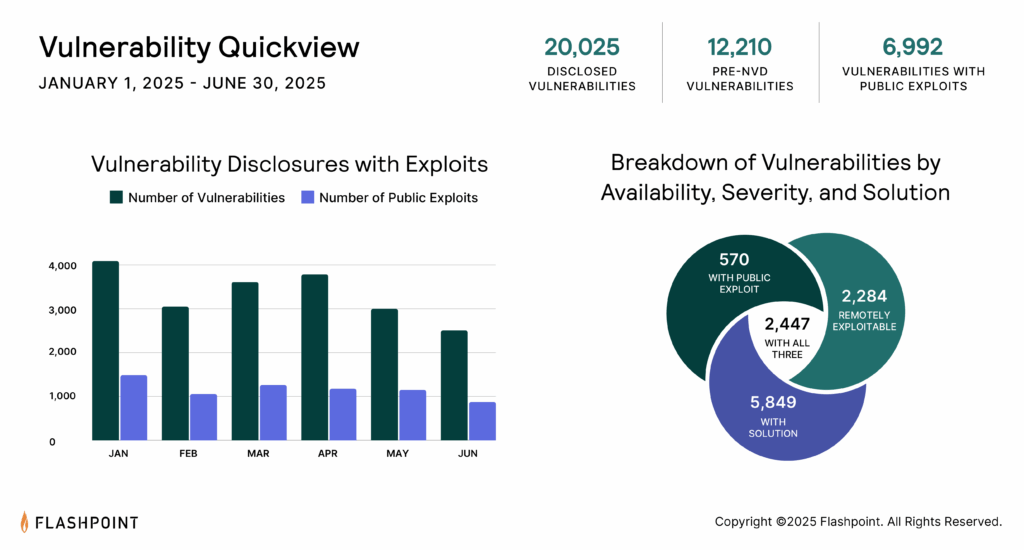
As seen in Flashpoint's Cyber Threat Intelligence Index, CVE and NVD consistently fail to report hundreds of vulnerabilities every month. Over time, this adds up. CVE/NVD misses over 99,500 known disclosed vulnerabilities. This means that organizations strictly relying on CVE may be completely unaware of almost a third of known vulnerability risk.
Understanding the Vulnerability Intelligence Lifecycle
To understand what creates this intelligence gap, it is essential to understand the vulnerability intelligence lifecycle. If the vulnerability intelligence powering your Vulnerability Management program is incomplete, your organization is at a greater risk of being compromised. To determine whether your organization is using an incomplete source, it is important to know the elements of vulnerability intelligence.
Vulnerability intelligence breaks down into three key functions:
- Vulnerability discovery
- Vulnerability research
- Vulnerability analysis
What is Vulnerability Discovery?
Vulnerability discovery is the process of researching a piece of computer software or hardware. The goal is to evaluate it for the presence of vulnerabilities. As an organization, you can only analyze the vulnerabilities you are aware of. It is impossible to reduce or fix risk that you never knew existed.
Vulnerability discovery is the first step in the vulnerability intelligence lifecycle. It is the most important. This is the foundation that will dictate the effectiveness of your vulnerability risk program.
In this stage, researchers discover and publish vulnerabilities. Then vulnerability databases (VDBs) can aggregate and build upon those disclosures. It is vital that the vulnerability intelligence you rely on knows that thousands of unique channels exist and actively monitors them.
The vulnerability discovery process breaks down further into two steps:
- Vulnerability sources
- Vulnerability monitoring
Vulnerability Sources
The more vulnerability sources you can identify, the more robust your vulnerability coverage becomes. Vulnerabilities are disclosed and published in a wide variety of ways. This includes mail lists, blogs, service sites like GitHub, websites catering to exploit disclosures, and more.
Vulnerability disclosures are published across social media, the deep web, researcher blogs, product bug trackers, code commits, and more. Since there is no single source, it is vital that organizations intelligently gather as many vulnerabilities as they can. This helps them know which to focus on.
Vulnerability Monitoring
In the scope of vulnerability intelligence, vulnerability monitoring is the act of keeping tabs on a wide variety of sources that produce vulnerability disclosures. This process includes identifying new disclosures. It involves determining if information is valid, normalizing the data, adding metadata, and then including it into the vulnerability feed. Mature vulnerability intelligence solutions then offer support for the data they aggregate. This ensures an organization understands and can better utilize that data.
This is a real challenge. Adding to the difficulty is that a single source can sometimes contain thousands of disclosed vulnerabilities. What sources, and how many, are you aware of and actively monitoring?
What is Vulnerability Research?
Vulnerability research is the process of researching vulnerabilities. This is done to determine if any of them affect your organization's systems.
While monitoring vulnerability sources, you must research the vulnerabilities that appear. You must determine if any affect your organization's systems. Does a vulnerability affect a vendor in your supply chain, or a product used by your organization? If it does, what versions of that product are also susceptible to that vulnerability? Is an exploit available? Can you install a patch or upgrade to fix it?
This function is not so simple. Vulnerability research can have different meanings and occur at different times. This depends on the role of the person performing it. The roles that can influence this are:
- Vulnerability researchers
- Vulnerability intelligence companies
- Security analysts at organizations
For a vulnerability researcher, it includes doing the initial examination and investigation into a piece of computer software or hardware. This item contains bugs that may allow for unintended privileges. Examples include Flashpoint's own vulnerability research team. This team has discovered and published vulnerabilities affecting the Honey and Bitwarden browser extensions as well as other widely used products.
For a vulnerability intelligence company, the term means the act of going through publicly disclosed vulnerabilities. This is done to determine if they are legitimate issues (or classifying them as NAV). It involves aggregating that data, and then normalizing it for use by other organizations.
Organizations face a unique problem during vulnerability research. For an analyst, the term may mean researching if disclosed vulnerabilities impact their assets and what risk is posed. This means that your vulnerability research functions depend on the comprehensiveness of what researchers and vulnerability intelligence companies do.
According to that definition, vulnerability intelligence companies should be doing more than just aggregating CVE data. They are also responsible for determining if issues are legitimate and enhancing it with rich metadata. But if you think back to the last vulnerability you researched, how detailed was it?
What is Vulnerability Analysis?
Vulnerability analysis is the last function of the vulnerability intelligence lifecycle. In this state, you measure the potential damage a vulnerability can cause if exploited. Ultimately, you are asking yourself, "Now that I know this affects me, how bad can it be?"
To better understand overall and potential risk, you need vulnerability metadata, severity information, and impact data.
Vulnerability Metadata
By definition, metadata is "a set of data that describes and gives information about other data." For vulnerabilities, metadata may include the location of the attacker, the attack type, the high-level impact, and the availability of a solution. It covers the status of an exploit, aspects of the disclosure, general types of technology represented, authentication requirements, and more.
Severity
The vulnerability severity refers to how serious, or how big of a risk, is associated with it. Low severity issues may not be prioritized. This is because they are not seen to pose much risk to an organization. High severity vulnerabilities are typically triaged and patched immediately.
Impact
When a vulnerability is exploited, it will impact a system in some manner. This may or may not be noticeable to administrators or users. At the highest level, confidentiality may be partially or fully impacted, for example. Impacting integrity can mean a variety of things. So, it may be described via simple metadata (e.g., the CIA triad) and with verbose descriptions that precisely lay out what happens if exploited.
Why is Vulnerability Intelligence Important?
In our State of Cyber Threat Intelligence report, we stated that hacking was the number one cause for data breaches. It accounted for over 60 percent of all reported compromise events. By taking advantage of flaws, hackers can gain a foothold into organizations. This creates chaos that can result in extreme financial loss. For this reason, having quality vulnerability intelligence is critical. It is needed to achieve an efficient vulnerability management program.
Knowing vulnerability details is important for determining the potential scope of damage. However, key metadata is often missing from most publicly accessible vulnerability entries and databases.
Unfortunately, many vulnerability intelligence vendors focus solely on collecting issues. They perform little to no quality checks. This results in inaccuracies and invalid entries. This means most security teams cannot spend their time on analyzing vulnerabilities. Instead, they are forced to spend more time validating entries and finding vulnerability metadata themselves.
What Should Vuln Intel Provide You?
Vulnerability intelligence should be comprehensive, detailed, and timely. Organizations need to be aware of everything in the vulnerability disclosure landscape. They must have all the details so that they can manage risk as soon as possible. But do they have that kind of visibility using CVE and NVD?
Just because the public source may not have those details, it doesn't mean that the information cannot be found. If your vulnerability intelligence feed consistently leaves out important metadata, it's likely that your intelligence provider is substituting vulnerability intelligence with CVE and NVD.
"We wanted to devote our scarce resources in actually doing something instead of just rating CVSS scores for vulnerabilities. Just knowing we have VulnDB inspires confidence. When you are exposed to it you know that this is quality information."
Stéphane Grundschober, Vulnerability Manager at Swisscom
Flashpoint's Comprehensive Vulnerability Threat Intelligence
Hopefully this guide has been helpful. It showed you what vulnerability intelligence is, and why every organization needs it. However, if you've begun realizing the shortcomings of your current intelligence vendor, you probably have more questions.
What's next? What does "good" vulnerability intelligence actually look like? Can I see it for myself? Check out the following resources to learn more:
- Flashpoint Weekly Vulnerability Insights and Prioritization Report
- Your Guide to Proactive Vulnerability Management
- The Buyer's Guide to Vulnerability Intelligence
- Everything You Need to Know About Vulnerability Management
- VulnDB: What comprehensive vulnerability intelligence looks like
- Datasheet: Why VulnDB?
- Case study: Swisscom Frees Up Limited Resources with Better Data
- Case study: VulnDB Enables Continuous Product Security for Dräger
Frequently Asked Questions (FAQ)
Q: What is vulnerability intelligence and how does it inform security?
A: Vulnerability intelligence is a specific type of threat intelligence focused on gathering, analyzing, and sharing information about software and hardware flaws. It provides the necessary context and data to inform an organization's vulnerability management program, allowing teams to prioritize and fix the highest-risk issues.
Q: What are the three core functions of the vulnerability intelligence lifecycle?
A: The lifecycle breaks down into three key functions: Vulnerability Discovery (finding the issues), Vulnerability Research (determining legitimacy and risk), and Vulnerability Analysis (gauging the potential damage using metadata like severity and impact).
Q: Why is relying solely on public sources like CVE and NVD insufficient?
A: Public sources like CVE and NVD are often insufficient because they consistently miss a significant number of known vulnerabilities (creating intelligence gaps) and often omit critical vulnerability metadata necessary for effective prioritization, forcing analysts to manually validate and research issues.
Get the latest news and insights delivered to your inbox.
Interested to see top news from Flashpoint hit your inbox directly? Subscribe to our newsletter to receive curated content on a regular basis.
