KEY TAKEAWAYS
- Between 16:20:43 UTC on November 6, 2016 and 8:19 UTC on November 7, 2016, Flashpoint observed four 30-second HTTP Layer 7 attacks targeting the campaign websites of presidential candidates Donald Trump and Hillary Clinton. There were no observed or reported outages for either of the sites.
- Flashpoint assesses that unsophisticated actors are using the Mirai Internet of Things (IoT) botnet to target the candidates’ websites; analysts do not believe that the attacks were related to nation-state interference in the November 8, 2016 presidential election.
- Flashpoint assesses with moderate confidence that the Mirai botnet has been fractured into smaller, competing botnets due to the release of its source code, which has led to the proliferation of actors exploiting the botnet’s devices.
- Flashpoint will continue to monitor the Mirai botnet for further developments.
Background
Distributed Denial of Service (DDoS) attacks are once again a major concern after the recent record-breaking attacks against “Krebs on Security”, French ISP and hosting provider OVH, and Dyn DNS — the latter which resulted in sweeping, extended outages for many popular websites on the East Coast. Each of these attacks was perpetrated with a botnet comprising Internet of Things (IoT) devices compromised via Mirai malware. These vulnerable IoT devices include digital video recorders, webcams, and baby monitors.
In early October, the release of the Mirai malware within a well-known underground forum has effectively proliferated its use across the amateur hacker community. This release has caused many hackers to compete with one another for control of IoT devices that remain susceptible to Mirai malware. In order for these hackers to launch large-scale DDOS attacks successfully — such as those we’ve seen against Krebs, OVH, and Dyn — they will need to outperform competitors who are vying to control the same type of devices. Though not impossible, overcoming this competition is a considerable challenge and so far, the IoT botnet landscape appears to be saturated with too many would-be controllers and not enough new vulnerable devices. Due to these factors, the botnet’s fracturing has significantly lowered the impact, efficacy, and damage of subsequent attacks since the Mirai source code’s release and the attack on Dyn.
Short series of attacks exacerbates election day concerns
Recently, political figures, analysts, and media alike have been concerned over the potential for Mirai botnet DDoS attacks during the upcoming United States election day. Although these botnets may have grown smaller and less effective, many hackers continue to attempt to use them to gain attention, build credibility, and/or create disruption.
Indeed, Flashpoint has recently observed a short series of Mirai botnet DDoS attacks against websites associated with the Democratic and Republican nominees for president. On November 6, at 16:20:43, Flashpoint observed a 30 second HTTP Layer 7 attack against the website “secure[.]donaldjtrump[.]com”, Republican nominee Donald Trump’s campaign website.
The next day, Flashpoint observed a separate and distinct set of attacks against Donald Trump’s campaign website with renewed attacks on the domain at 8:13 UTC, 8:16 UTC, and 8:19 UTC. In this instance, hackers also targeted Hillary Clinton’s campaign website; the last attack at 8:19 UTC was against “hillaryclinton[.]com.” While each of these attacks appear to be distinct and powered by different groups, they were all perpetrated using Mirai-based botnets, all categorized as HTTP layer 7 attacks, and all lasted for 30 seconds.
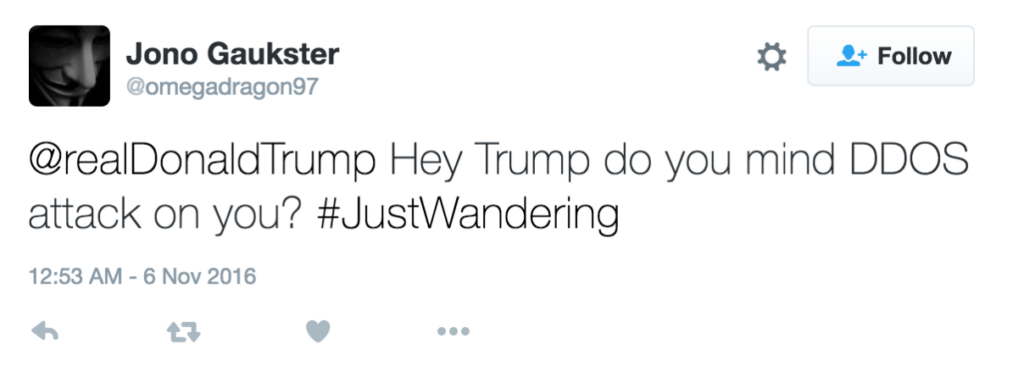
At least one known hacker has claimed credit for the first set of attacks against Donald Trump’s campaign website, although this claim cannot be independently verified. Jono Gaukster (@omegadragon97) tweeted to Donald Trump’s twitter handle (@realDonaldTrump) just 30 minutes after the attack.
Electoral process infrastructure remains unaffected
So far, these DDoS attacks been limited to the nominees’ website infrastructure and have not targeted – nor affected – any infrastructure associated with the actual electoral process. Flashpoint assesses with high confidence that these attacks were not perpetrated by a state actor. This attack, in addition to other more powerful, higher-profile attacks associated with the Mirai botnet, all align closely with tactics, techniques, and procedures commonly executed by hackers operating from underground forums.
Though these attacks’ targets suggest political motivation, this may not be the case. Widespread concerns of DDoS attacks surrounding election day provide fertile ground for hackers operating from underground forums, as these hackers tend to be primarily motivated by the desire for attention, credibility, or “trolling” via disruption and chaos. This election season seems to be particularly contentious, and fears over foreign influence in the election have only raised anxieties surrounding election day.
While attacks against websites may cause minor challenges for the respective candidates’ campaign operations, they will not directly impact the final vote count in the presidential election on November 8. Flashpoint will continue to monitor the Mirai botnet for further developments.


