Blog
Insider Threat: How to Identify, Prepare For, and Prevent Insider Threats
Organizations must evolve their capability to identify, respond to, and mitigate insider threats, which can come in a number of forms
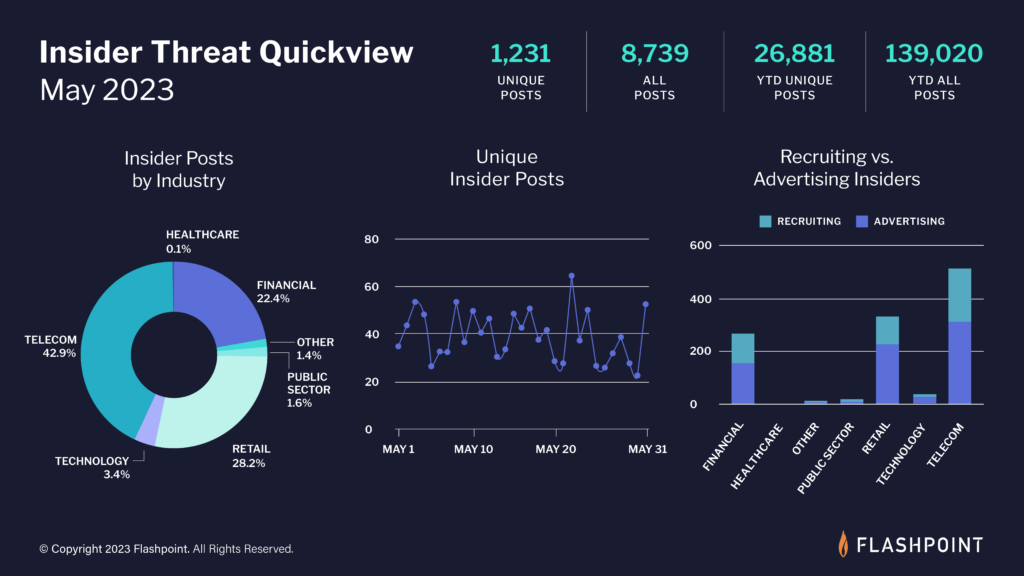
Insider threats on the rise
The tactic of recruiting insiders has been gaining popularity among threat actors aiming to breach systems and/or commit ransomware attacks. According to Flashpoint data collections, there were 3,988 unique discussions about insider-related threats observed in our datasets between January 1 and November 30, 2021—a number that shows dramatic growth since August 2021. Furthermore, a January 2022 study found that 65 percent of employees had been approached by malicious actors, often to aid in a ransomware attack, for a hefty cash reward, which represents a double-digit increase from the prior period.
Running parallel to the increasing threat of malign corporate insiders, threat actors adapt and modify the tactics they use to solicit these insiders. As a result, businesses must follow suit and evolve their capability to identify, respond to, and mitigate insider threats, which can come in a number of forms.
Types of insiders
While this article focuses on the recruitment of malicious insiders, it’s important to outline the larger insider threat landscape, which includes risk apertures that are not necessarily opened by an insider for the prospect of a payout. As such, there are multiple types of potential insiders within an organization, including careless workers, disgruntled employees, and third parties. Each of them can be placed into one of the following categories:
- Accidental insiders: An insider who takes inappropriate and potentially dangerous action unknowingly and without the intent to harm. They have no motive and have not consciously decided to act.
- Negligent insiders: An insider who is not intentionally harming the organization, but has made the decision to take risky action with the hope that it will not materialize into a threat. The have no motive but have consciously decided to act inappropriately.
- Malicious insiders: An insider who is knowingly takes action to harm the organization. They most likely have some motive, be it financial or related to a personal grievance, and have made the conscious decision to act on it.
Recommended Reading: The Insider Threat Intelligence Cycle
It is important as an organization to not only defend employees from the threat actors trying to recruit them, but also to implement offensive measures that position them to independently understand how to work safely and avoid risk. These measures may include:
- Employee education initiatives that focus on teaching employees about threat actor TTPs, how to detect them, and what to do if they suspect they are being targeted.
- A strong threat intelligence program that keeps the organization aware of new risks and TTPs to watch out for, and gives your security teams the ability to intercept threats before they reach employees.
- Limiting employee accessibility to any data or infrastructure they do not need to do their job, which minimizes the access they can give threat actors.
How threat actors recruit insiders
Threat actors may recruit corporate insiders to perform malicious actions on their behalf and/or provide them with remote network access. Flashpoint analysts have observed the following primary categories of threat actors involved in insider recruitment:
- Fraudsters
- Ransomware groups
- Non-ransomware extortionist groups
These threat actor categories have been observed employing the following tactics to recruit corporate insiders:
- Using a known insider—one gained through personal relationships
- Conducting online recruitment via:
- Public recruitment advertisements
- Direct solicitation
- Fake candidate scams
- Insiders may also advertise their ability to act maliciously on behalf of threat actors
Recommended Reading: Demystifying Insider Threat
Who is recruiting?
Fraudsters
Threat actors involved in fraud activity make up the bulk of insider recruiters observed by Flashpoint. In general, these threat actors are interested in recruiting insiders who can either provide direct or indirect access to corporate systems, and/or perform illicit actions on their behalf. Typically, fraudsters use insiders for the following attack vectors:
- Account takeover (ATO) attacks
- Two-factor authentication (2FA) bypass
- SIM swapping attacks
- Fraudulent account creation
- Fraudulent loan applications
- Facilitation of fraudulent transactions
Ransomware groups
As ransomware continues to be a persistent problem faced across all sectors, the groups and actors behind these attacks are continually seeking new ways to gain remote access to victim networks. One of the methods ransomware groups use to facilitate access and installations is recruiting insiders. Since 2020, the following instances of ransomware groups or actors leveraging insiders have been identified:
- In December 2021, the FBI announced the arrest of Nickolas Sharp for his role in a data breach at Ubiquiti reported in January 2021. Sharp both exfiltrated data from Ubiquiti and demanded a ransom from the company to return the data.
- In August 2021 the ransomware gang LockBit recruited potential insiders in a message posted on encrypted devices, likely targeting IT consultants.
- Also in August 2021, Abnormal Security researchers identified threat actors who claimed to be connected to the Nigerian ransomware collective “DemonWare” and offered an organization’s employers up to US$1 million to install ransomware on their network.
- In July 2021 the possibility was discussed that the zero-day vulnerability used in the Kaseya supply chain attack was leaked to the REvil ransomware gang by a corporate insider. It had emerged that Dutch researchers had warned the company of the vulnerability months before the attack.
- In August 2020 the FBI arrested Egor Kriuchkov, a Russian national who tried to recruit an insider at Tesla to exfiltrate information from a company server.
Non-ransomware extortionist groups
Non-ransomware extortionist groups rely on data exfiltration and the threat of data leaks to extort victim organizations. The extortionist group LAPSUS$ provides a prolific recent example of insider recruitment for this purpose. The group was responsible for successfully exfiltrating data, including source code, from a number of global technology companies. LAPSUS$ was successful in recruiting insiders in large corporations who could provide access to corporate virtual private networks (VPNs) and/or help bypass multi-factor authentication.
Recruitment tactics
When recruiting insiders, threat actors typically have two primary options:
- They can work with someone they know in the physical world (typically a friend, relative, or colleague), or
- They can set up a digital relationship with someone by recruiting them online, often through monetary incentives.
Known Insider
Threat actors working with insiders they know in the physical world likely have higher levels of trust, based on both the prior relationship and the fear of repercussions, since each person’s identity is known to the other. A disadvantage of working with a known insider is that if one person is caught, their co-conspirators are also likely to be identified.
Online insider recruitment
Threat actors who recruit online have more difficulty confirming the credibility and trustworthiness of potential partners; however, the talent pool is much broader online and the range of possible targets is exponentially larger. It is also less likely that the threat actor will be identified if their insider connection is caught.
Recommended Reading: The Great Cyber Exit: Why the Number of Illicit Marketplaces Is Dwindling
Public recruitment advertisements
Threat actors often broadcast their request for corporate insiders within fraud-related illicit online communities in the hopes that an insider will see and respond to the solicitation. LAPSUS$ used this method, posting requests for insiders in its Telegram group.
Direct solicitation
In the direct solicitation method, threat actors send messages directly to corporate employees via emails, phone calls, text messages, social media, or chat platforms.
In one example from August 2021, threat actors behind the DemonWare ransomware attempted to initiate a conversation with corporate employees via email, requesting that employees install DemonWare ransomware on corporate computer systems in exchange for 40 percent of the ransom proceeds. The threat actors also provided a secondary email and their Telegram handle in order to move the conversation to an off-band communication medium out of the control of the victim company.
Fake candidate scams
In a fake candidate scam, a job candidate uses false information to attempt to obtain a position in the company. These candidates may misrepresent themselves via resumes or interviews to get a job they would not otherwise be offered. In rare cases, fake candidates may use others to interview on their behalf to land the job. The intent behind obtaining a position at the company is to operate as a malicious insider upon gaining access to the corporate network.
Although fake candidate scams existed before COVID-19, the rise in remote work has led to an increase in these scams. Additionally, there are reports that recruiting services may implement aspects of the fake candidate scam to place their clients into companies.
Common signs of a fake candidate are:
- Perfect resumes for the position—resumes that have too many in-demand skills for a job position and are too strong may signal misrepresentation.
- Missing or partial contact information, which may be an attempt to obfuscate the applicant’s identity and avoid a successful background check.
- Date incongruities across application submissions and other profiles, which could indicate the applicant is making errors in their attempt to create a cohesive narrative.
- Social media profiles or profiles that do not match the provided information.
- Outreach
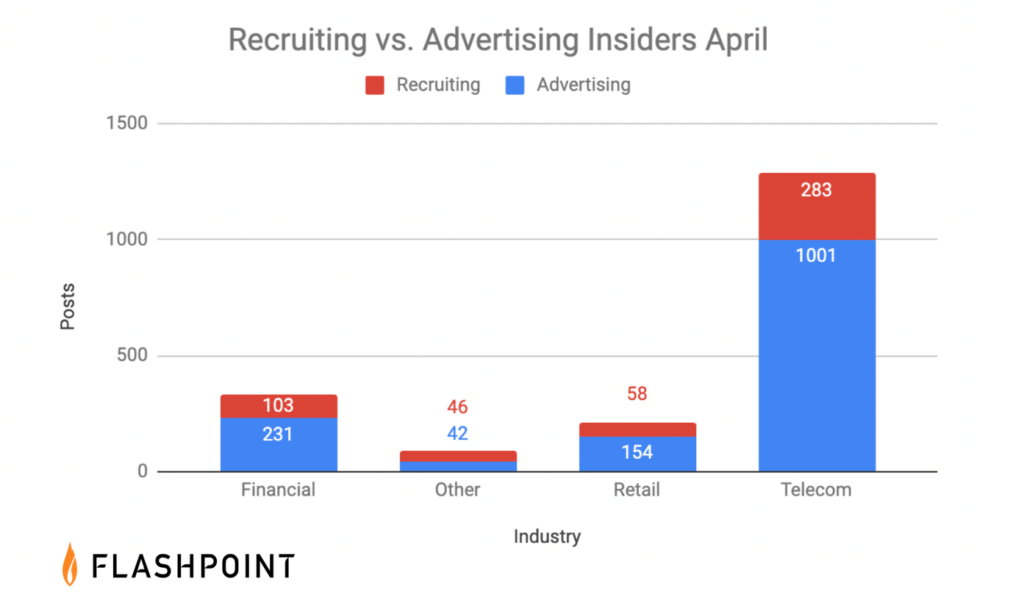
- Insider activity has flourished on messaging platforms with channels and groups dedicated to insider activity, though the activity tends to be focused on retail (carding and other forms of fraud) and mobile telecommunications (SIM swapping).
Insiders post messages on messaging platforms advertising themselves as insiders and declaring themselves ready to work on various schemes for a fixed price or share of the profits. Flashpoint has identified several examples of both public insider recruitment advertisements followed by outreach from claimed insiders within the LAPSUS$ Telegram group chat.
It is possible that insiders may claim to have access to a victim corporate network as a form of outreach. However, unless the individual specifically claims to be an insider or shares further details through a direct engagement, these cases of outreach are not discernable from threat actors who have illicitly purchased or otherwise gained access to a victim network.
Suppress corporate data theft with Flashpoint
Responsible for detecting, deterring, and mitigating threats arising from the misuse of authorized access to an organization’s network, systems, or assets, insider threat programs (ITPs) require extensive resources in order to operate effectively. Start your free trial to see how Flashpoint can help you combat insider threats today.

